Data Masking is a technique for creating a fictitious but realistic representation of your company’s data. When genuine data such as in User Training, Sales Demos, or Software Testing isn’t needed, then the purpose is to secure sensitive data while offering a functioning replacement. Data masking processes alter the data’s values while maintaining the same format. The idea is to develop a version that is impossible to interpret or reverse engineer. Character Shuffling, Word or Character Substitution, and Encryption are all options for changing the data.
Masking data is the process of changing readable data into unreadable data that, until proper authorization to retrieve original data, no one can use or access. The technique of masking data is also a power tool for privacy with regulations and risks-reduction. However, with the numerous techniques of masking available—encryption, substitution, and so on—it is tough to know which technique will work better for an organization.
In this blog, I will take you through some of the most common data masking techniques and also provide best practices that enable choosing the right solution for each case. Whether you are at the starting point of using data masking or want to add strength to your existing strategy, let me guide you on how you can keep your data safe. Let’s get started!
Table of Contents
What is Data Masking?
- Data Masking, also known as Data Obfuscation, hides the actual data using modified content like characters or numbers.
- The main objective of Data Masking is creating an alternate version of data that cannot be easily identifiable or reverse-engineered, protecting classified Data as sensitive.
- Importantly, the data will be consistent across multiple Databases, and the usability will remain unchanged.
There are many types of data that you can protect using masking, but common data types for Data Masking include:
- PII: Personally Identifiable Information
- PHI: Protected Health Information
- PCI-DSS: Payment Card Industry Data Security Standard
- ITAR: Intellectual Property
Data Masking is most commonly used in non-production contexts, such as Software Development and Testing, User Training, and so on, areas where actual data isn’t required. You can mask using a variety of ways, which you’ll go through in the subsequent sections of this tutorial.
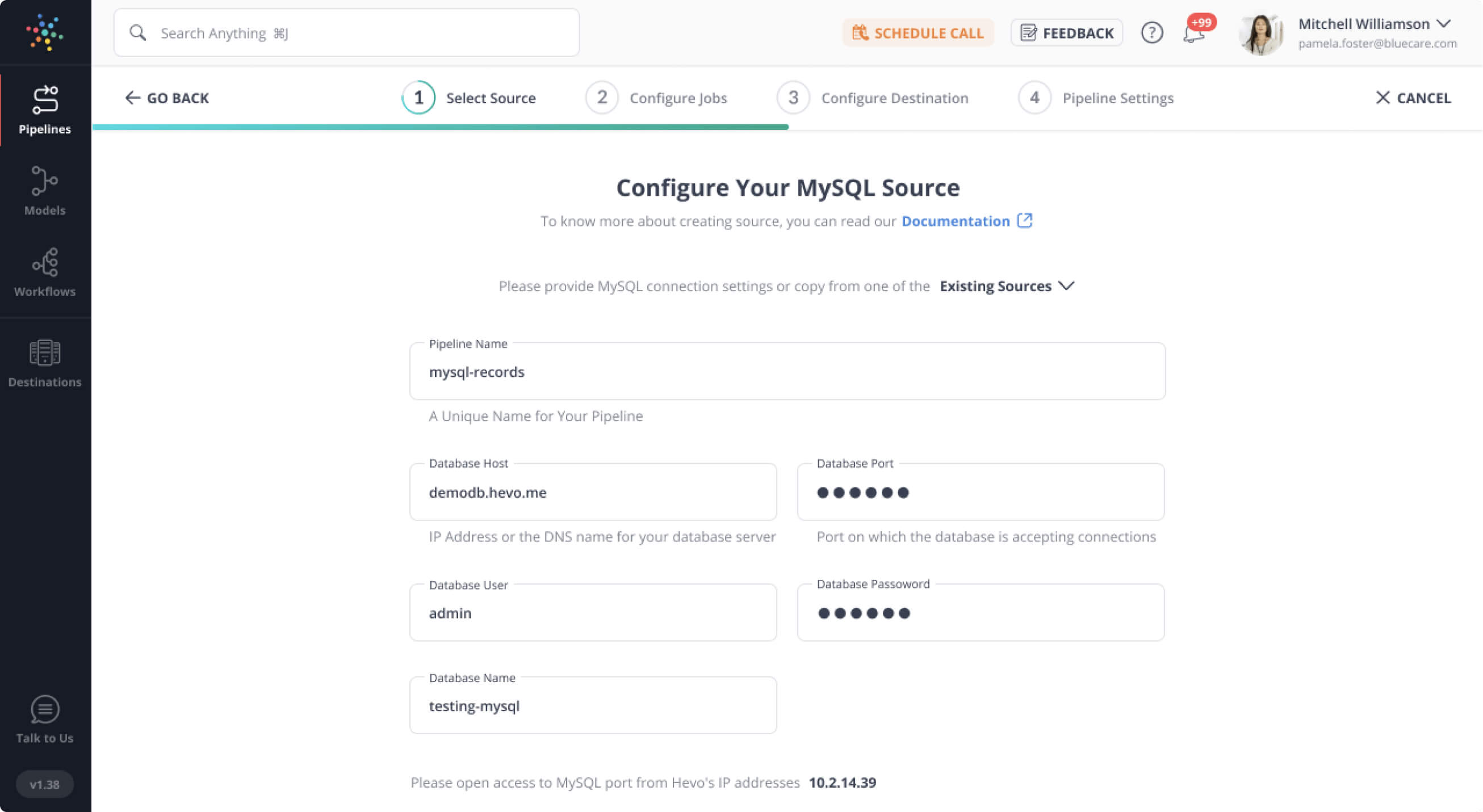
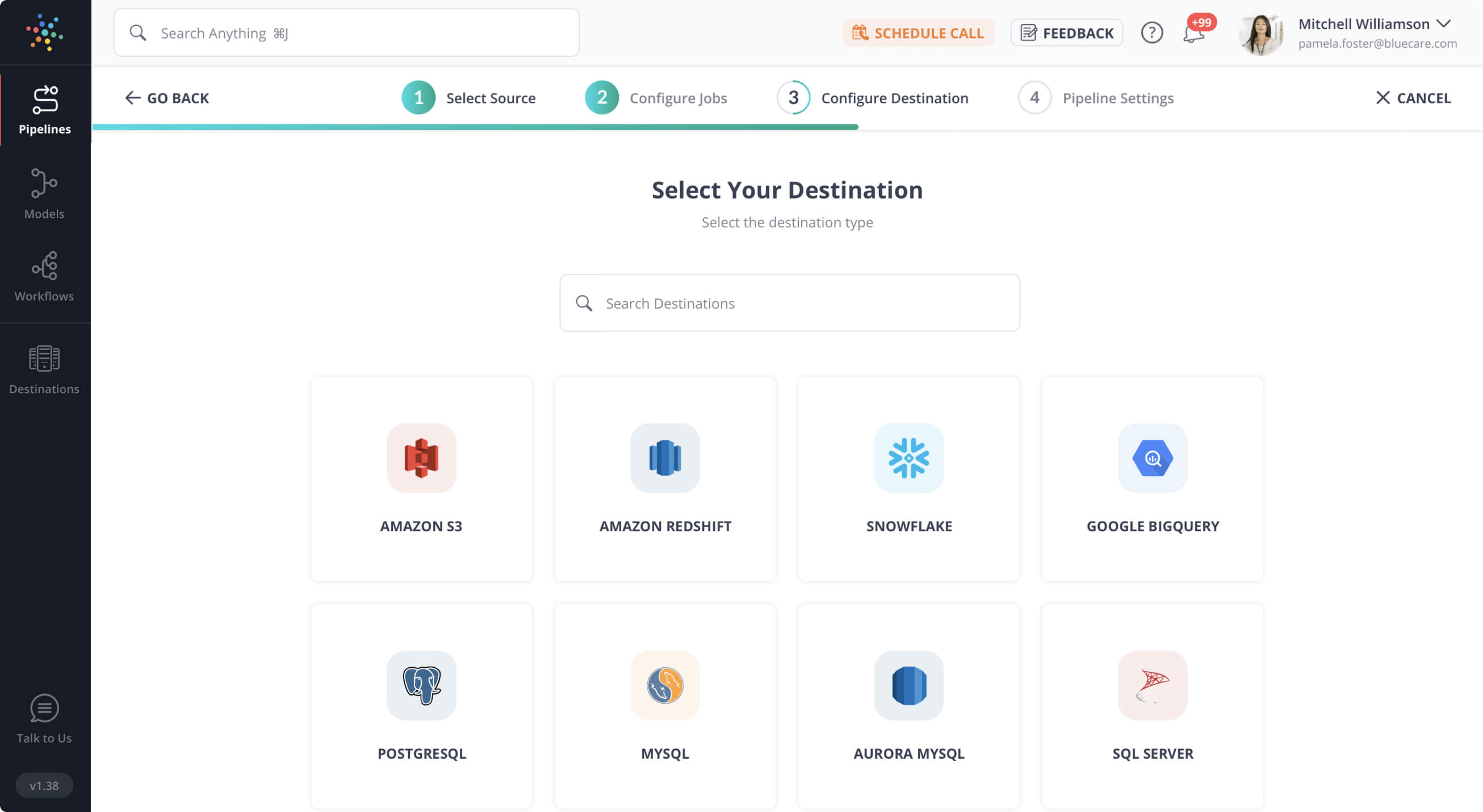
Hevo Data, a fully managed data Pipeline platform, can help you automate, simplify & enrich your data replication process in a few clicks without compromising the security of your data. Here’s why you should give Hevo a try:
- All connections to Hevo UI are encrypted through HTTPS
- Risk management and security framework for cloud-based systems with SOC2 Compliance.
- 24/5 Live Support via chat, email, and calls.
Try it out yourself and see why healthcare industry leaders like Curefit prefer Hevo to ensure zero data loss and seamless integration.
Get Started with Hevo for FreeWhy is Data Masking needed?
Data masking is necessary for many organizations for the following reasons:
- Removing the risk of sensitive Data Disclosure assists businesses in remaining compliant with the General Data Protection Regulation (GDPR). As a result, Data Masking provides a competitive edge for many businesses.
- Makes data unusable for cybercriminals while keeping its Consistency and Usability.
- Data Masking addresses a number of significant dangers, including Data Loss, Data Exfiltration, insider threats or account breach, and insecure Third-Party system Interfaces.
- It allows authorized users, such as testers and developers, to access data without exposing production data.
- Data Sanitization is possible because conventional file deletion leaves traces of data on storage media, whereas sanitization masks the old values.
- Avoids the dangers of outsourcing any project. Masking protects data from being exploited or stolen because most firms rely solely on trust when working with outsourced personnel.
Types of Data Masking
1) Static Data Masking
- Static Data Masking is most commonly used on a production database backup. SDM alters data to make it appear accurate so that it may be developed, tested, and trained accurately, all without revealing the true facts.
- The procedure is as follows:
- Make a backup or a golden copy of the production database and move it to a new location.
- While in stasis, remove any unneeded data and disguise it.
- Save the masked copy where you want it.

2) Dynamic Data Masking
- Dynamic Data Masking occurs dynamically at runtime and feeds data directly from a production system, eliminating the requirement to save masked data in a separate database.
- It is generally used to process Role-Based Security for applications such as customer service and medical records management. As a result, DDM is used in read-only settings to prevent the masked data from being written back to the production system.
- DDM can be implemented with the help of a Database Proxy, which alters queries sent to the original database and sends the masked data to the requesting party. You don’t have to construct a masked database ahead of time with DDM, but the application may have performance issues.

Also Read: Snowflake Data Masking
3) Deterministic Data Masking
- Column Data is replaced with the same value in Deterministic Data Masking. For example, if your databases have a first name column that spans numerous tables, there could be many tables with the same first name.
- If you mask ‘Adam’ to ‘James,’ you should appear as ‘James’ in all connected tables, not just the masked table. The masking will give you the same result every time you run it.
4) On-the-Fly Data Masking
- When data is transferred from one environment to another, such as tests or development, On-the-Fly Data Masking happens.
- On-the-fly data Masking is appropriate for organizations that:
- Continuously Deploy Software
- Have a lot of Integrations
- Since maintaining a continuous backup copy of masked data is difficult, this method will only communicate a portion of masked data when it is required.
5) Statical Data Obfuscation
- Different Statistical Information can be hidden in production data using Statistical Data Obscuration techniques.
- Differential privacy is a strategy for sharing information about trends in a dataset without revealing information about the dataset’s actual members.
What are different Data Masking Techniques?
1) Data Encryption
- Data Encryption is the most difficult and secure method of Data Hiding. Here, you employ an encryption method to conceal the data and decrypt it with a key (encryption key).
- Data Encryption is better for data in production that needs to be restored to its original state. The data, on the other hand, will be safe as long as only authorized individuals have access to the key.
- If the keys are compromised, any unauthorized party can decrypt the data and access the raw data. As a result, appropriate Encryption Key Management is critical.
2) Data Scrambling
- Data Scrambling is a simple masking technique that jumbles the Characters and Integers into a Random Order, thereby disguising the original material.
- Although this is a simple strategy to use, it can only be used with particular types of data and does not make sensitive data as secure as you might anticipate. When an employee with ID number 934587 in a production environment undergoes Character Scrambling, the result will be 489357 in a different environment.
- However, anyone who remembers the initial order may still be able to figure out what it was worth.
3) Data Substitution
- Data Substitution is the process of disguising data by replacing it with another value. This is one of the most successful Data Masking strategies for preserving the data’s original look and feel.
- The substitution technique can be used with a variety of data types. For example, using a random lookup file to disguise customer names.
- Although this can be tough to implement, it is an effective method of preventing Data Leaks.
4) Data Shuffling
- Data Shuffling is identical to a replacement, except that it employs the same individual masking data column for randomized shuffling. For example, shuffle the columns of employee names among numerous employee entries.
- Although the generated data appears to be accurate, it does not expose any personal information. Shuffled data, on the other hand, is vulnerable to reverse engineering if the shuffling technique is discovered.
5) Nulling Out
By assigning a Null Value to a data column. Nulling Out masks the data so that any unauthorized user cannot view the actual data. This is another simple strategy, although it has the following drawbacks:
- Data Integrity is compromised.
- It’s more difficult to test and develop with such data.
6) Value Variance
- A function is used to replace the Original Data Values, such as the difference between the lowest and highest value in a series.
- If a buyer bought numerous items, the purchase price could be substituted with a range between the highest and lowest price paid.
- Without exposing the original dataset, this can provide helpful data for a variety of reasons.
7) Pseudonymization
- A new term, pseudonymization, has been created by the EU General Data Protection Regulation (GDPR) to include methods such as Data Masking, Encryption, and Hacking to secure personal data.
- Pseudonymization, as defined by the GDPR, is any process that prevents data from being used to identify individuals. It necessitates the removal of direct identifiers, as well as the avoidance of multiple identifiers that, when combined, can be used to identify a person.
- Encryption keys, as well as any other data that can be used to restore the Original Data Values, should be kept separate and secure.
8) Data Ageing
- Based on a stated Data Masking strategy with an allowable date range, this masking approach either raises or decreases a date field.
- For example, changing the date ‘1-Jan-2021′ to ‘07-Apr-2018‘ by 1000 days would result in the date ‘1-Jan-2021′ becoming ’07-Apr-2018.’
Best Practices for Data Masking
1) Determining Project Scope
- Companies should know what information needs to be safeguarded, who is authorized to see it, which Apps use the data, and where it sits, both in production and non-production domains, in order to perform Data Masking properly.
- While this may appear simple on paper, due to the complexity of operations and various lines of business, this procedure may need a significant amount of time and should be scheduled as a separate project stage.
2) Identifying the Sensitive Data
- Masking is not required for any of a company’s Data Elements. Instead, in both production and non-production situations, properly identify any existing sensitive data. This could take a long time, depending on the intricacy of the data and the organizational structure.
Identify and catalog the following items before masking any data:
- Location of Sensitive Data
- They can only be viewed by those who have been given permission to do so.
- Their Uses
3) Ensure Referential Integrity
- Each “kind” of information originating from a Business Application must be masked using the same procedure, according to Referential Integrity.
- It’s impossible to employ a single Data Masking technique throughout the entire enterprise in large organizations.
- Due to Budget/Business requirements, various IT administration methods, or different Security/Regulatory requirements, each line of business may be required to establish its own Data Masking.
- When dealing with the same type of data, make sure that different Data Masking techniques and processes are synced across the business. This will make it easier to use data across business divisions in the future.
4) Securing Data Masking Techniques
- It’s crucial to think about how to protect the Data-Generating Algorithms, as well as any alternative data sets or dictionaries that might be used to scramble the data.
- These algorithms should be considered extremely sensitive because only authorized individuals should have access to genuine data.
- Someone can reverse engineer big chunks of sensitive information if they figure out which Repetitive Masking strategies are being employed.
- Separation of roles is a Data Masking best practice that is explicitly required by some rules. For example, IT security personnel establish which methods and algorithms will be utilized in general, but individual algorithm settings and data lists should only be available to data owners in the relevant department.
Conclusion
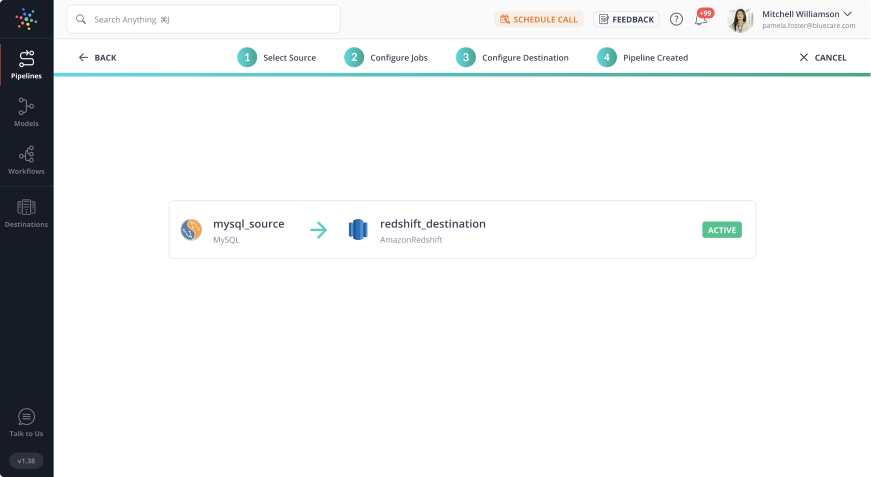
As organizations expand their businesses, managing large volumes of data becomes crucial for achieving the desired efficiency. Data Masking powers stakeholders and management to handle their data in the best possible way. In case you want to export data from a source of your choice into your desired Database/destination then Hevo Data is the right choice for you!
Want to take Hevo for a spin? Sign Up for a 14-day free trial and experience the feature-rich Hevo suite firsthand. You can also have a look at the unbeatable pricing that will help you choose the right plan for your business needs.
Share your experience learning about data masking! Let us know in the comments section below!
FAQs
1. What is the difference between data masking and encryption?
In data masking, sensitive information is replaced with fictional data, making it unreadable, whereas encryption scrambles data and can only be read by someone with a decryption key. Masked data cannot be restored to its original form, unlike encryption.
2. What is the key advantage of data masking?
The most important benefit from using data masking is that it allows use of data for testing or analysis in a safe manner that does not reveal the original sensitive information because the masked data cannot be unmasked.
3. Can masked data be unmasked?
No, masked data can’t generally be reversed back to its form before masking. Therefore, masked data is quite different from encryption, which may be decrypted with the appropriate key.